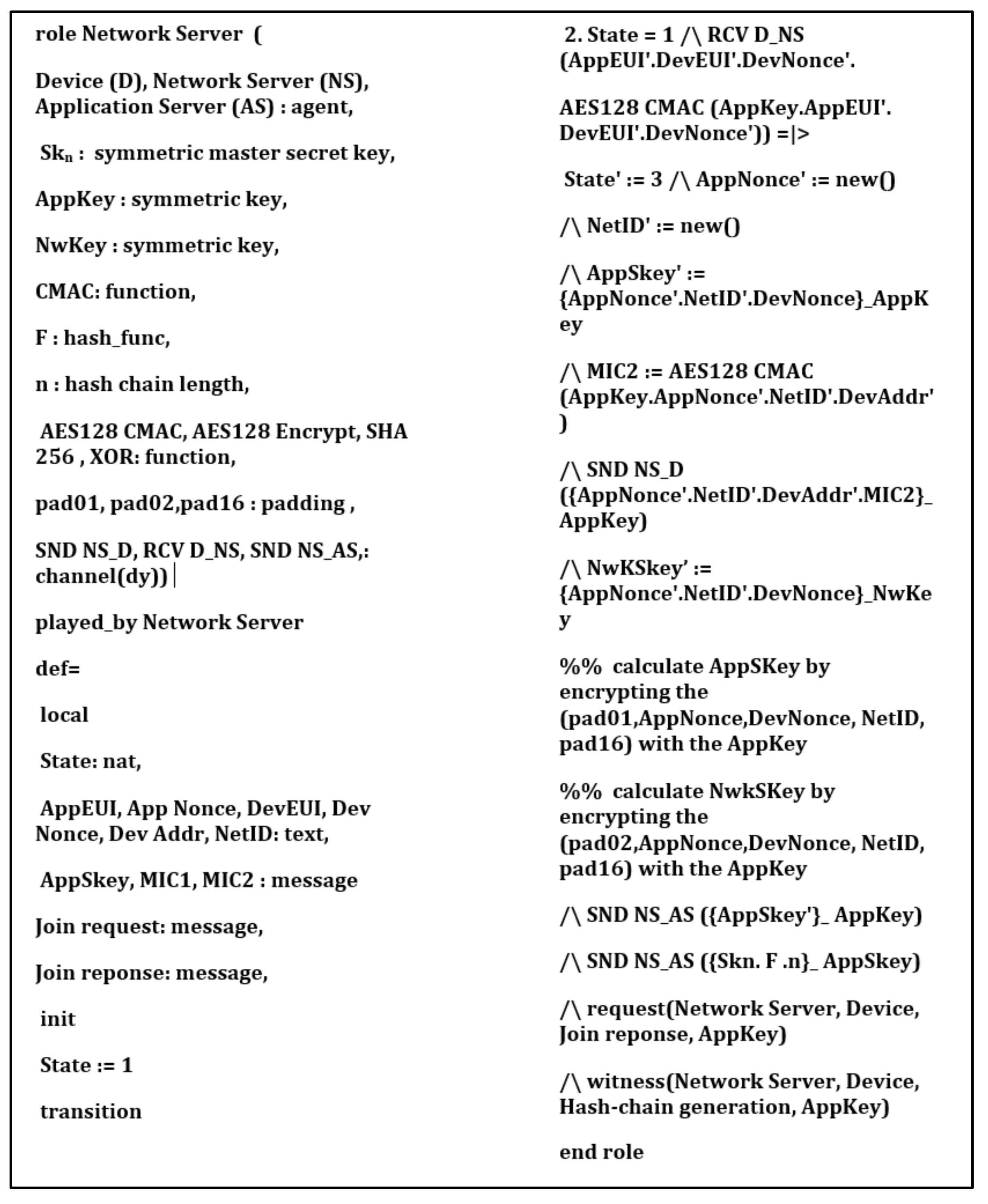
Sensors | Free Full-Text | A Key Management Protocol Based on the Hash Chain Key Generation for Securing LoRaWAN Networks | HTML
How to navigate GradApp to apply for the Certificate: Foundations for Biomedical Science PhD's Serving Indigenous Cultures (P